Virtual Card Reimbursements: Where Posting Breaks Down (And How STP Fixes It)
Top Takeaways
- Virtual card reimbursements promise faster, digital payments for physician groups but often involve cumbersome manual workflows that undermine efficiency.
- Traditional posting processes for virtual card payments create multiple opportunities for errors, delays, and lost revenue—especially when mail, portals, and manual reconciliation are involved.
- Straight Through Processing (STP) offers a streamlined solution, enabling physician groups to improve payment posting without overhauling existing systems.
If you lead finance or operations for a physician group, you’ve probably heard virtual card reimbursements pitched as a faster, more modern alternative to paper checks.
On the surface, virtual card payments are digital, automated, and convenient. Under the hood, they often behave very differently.
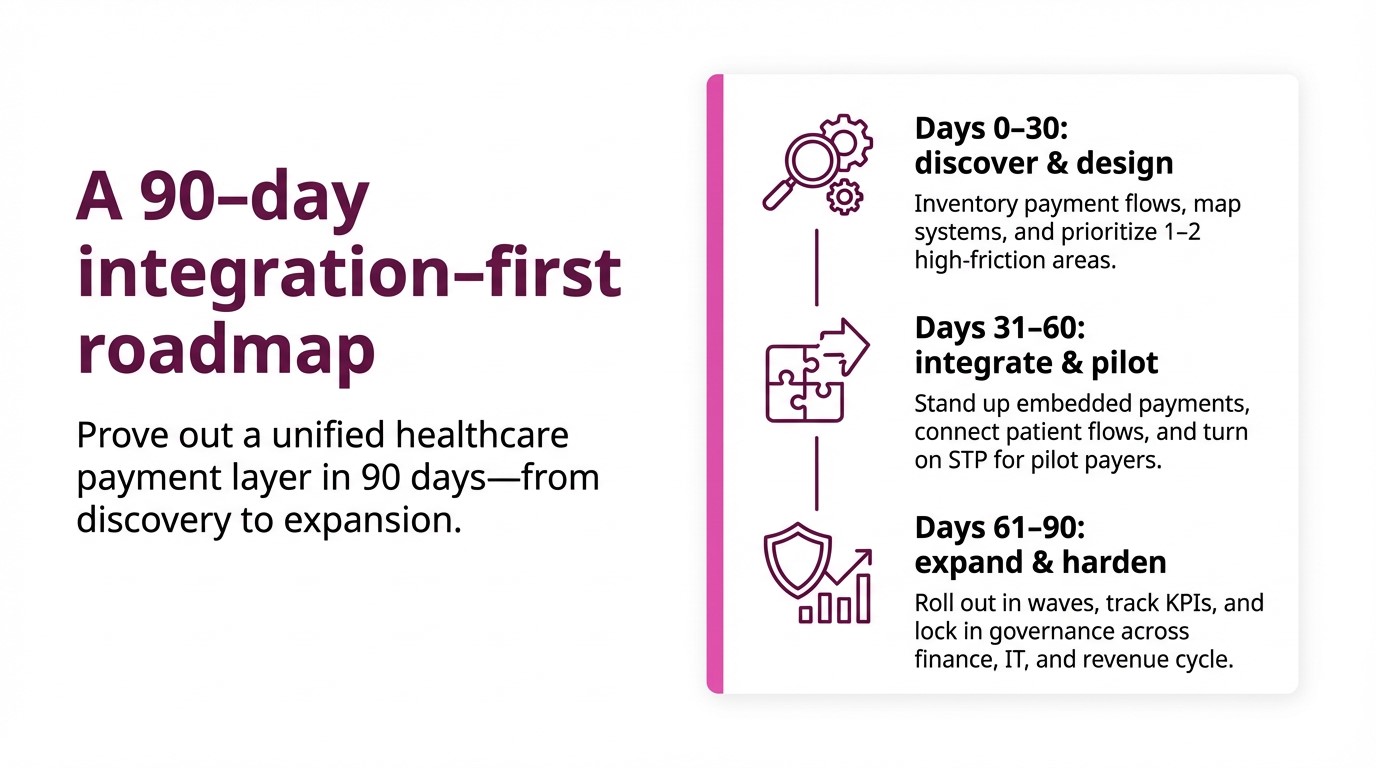
Across multi-site physician groups, Optum and other payer virtual cards still commonly move through mail, portals, terminals, and spreadsheets before they ever become clean, posted cash in your ledger. That “last mile” from approved to deposited + reconciled is where reimbursement performance quietly breaks down.
This post looks at:
- Where posting fails for virtual card payments today
- Why that failure is especially painful for physician groups
- How CSG Forte’s Straight Through Processing (STP) fixes it—without forcing you to rip and replace core systems
Where posting breaks down
Those steps create several predictable failure points for virtual card payments in physician groups.
1. Card credentials instead of a postable transaction
A mailed virtual card letter or portal credential is not a transaction—it’s an instruction set your team has to turn into cash. Someone must:
- Retrieve the credentials
- Run the card
- Find the associated remittance
- Decide how to post it
Each hand-off adds latency and operational risk.
2. Funds and remittance travel separately
Deposits and detailed remittance data often do not arrive together. Teams may see bank credits long before a usable remit, or vice versa. The gap drives:
- Unapplied cash
- Misapplied payments
- Manual research at month-end close
3. One card, many claims
A single virtual card can bundle multiple patients, claims, locations, or specialties. Without a reliable way to tie that card to structured remittance at the moment it lands, your staff are forced into manual, line-by-line allocation.
4. Fragmented workflows across clinics and specialties
Different clinics and specialties often evolve their own rules for handling virtual card payments—different portals, spreadsheets, reconciliation tricks and fee assumptions. The enterprise impact:
- No single view of the true cost of virtual cards (fees + labor + backlog)
- Higher audit and compliance risk from inconsistent controls
5. Expanded PCI and security exposure
Mail-and-portal workflows push card credentials and remittance information onto desks, into inboxes and across shared drives. Internal guidance notes that this widens your PCI DSS footprint and increases the surface area for fraud and error compared with a controlled electronic flow.
6. Human-driven exceptions
Because humans drive every step, exceptions are everywhere:
- Amount mismatches and unexpected adjustments
- Missing or incomplete remittance data
- Incorrect routing by TIN, entity or location
Instead of a manageable exception queue, you get daily fire drills, “mystery deposits” and rework that lands on your most experienced team members.
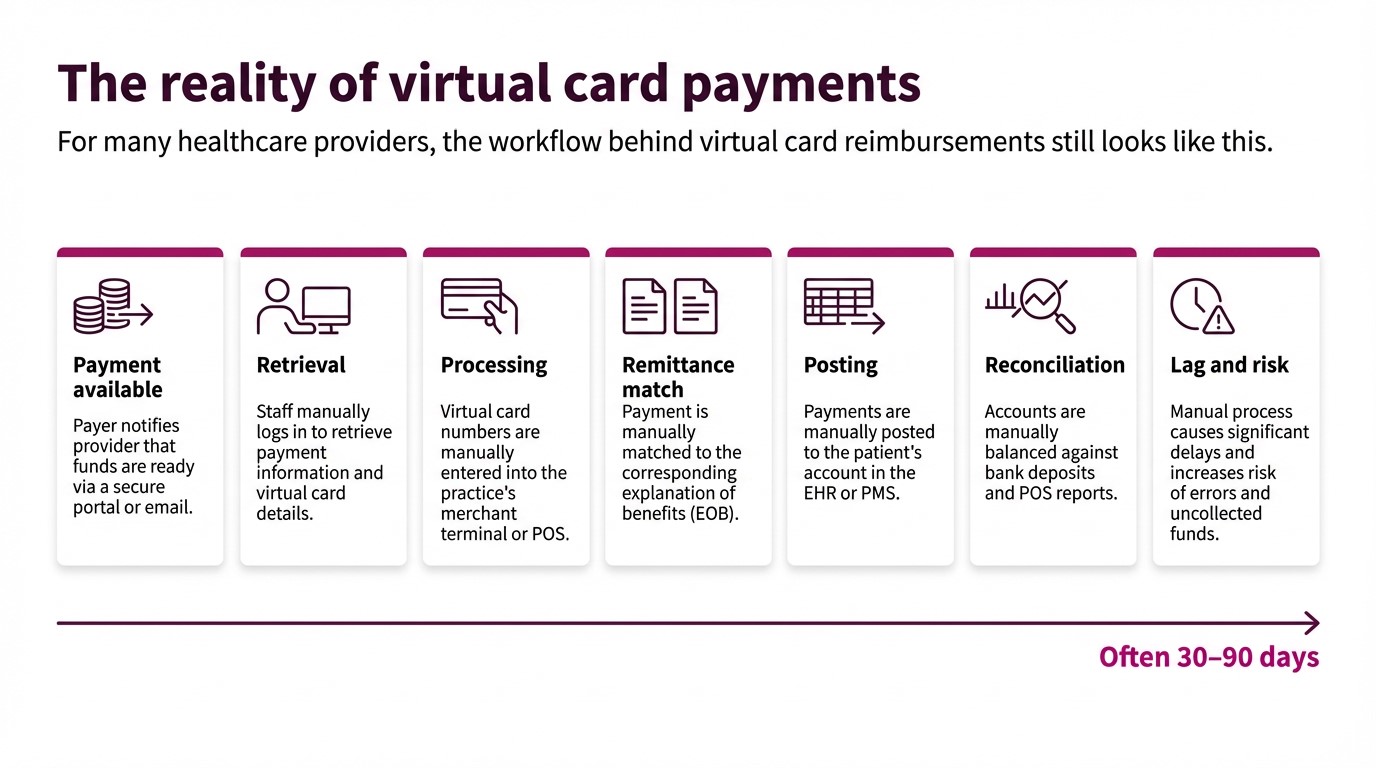
What STP does for virtual card payments
STP is defined internally as a payment automation process that allows healthcare providers to receive payments from insurance companies—and from patients via payer portals—in about one day, directly into their bank accounts.
Crucially for posting, STP focuses on the last mile of virtual card payments, not claim adjudication.
In the Optum + CSG Forte model, STP keeps the payer’s virtual card construct, but automates what happens next:
- The payer or Optum issues a virtual card for an adjudicated claim (or patient balance) exactly as they do today.
- Instead of printing and mailing, card credentials + remittance data are sent electronically to CSG Forte over secure, encrypted channels.
- CSG Forte processes the virtual card automatically—no manual keying.
- Funds are deposited directly into the provider’s bank account, typically the next business day, based on configuration and funding cycles.
- Payment and remittance data are delivered together in a format that supports auto-posting and streamlined reconciliation in your revenue and finance systems where integrated.
Result: one integrated flow from “payment available” to deposited, posted, and visible, without envelopes, portals, or duplicate data entry.
Questions to ask as you evaluate STP
You can frame internal and vendor conversations around a few practical questions:
- Volume: Which payers and programs generate the highest share of your virtual card payments today?
- Latency: How long, on average, does it take to move from “payment available” to deposited and posted cash for those streams?
- Effort: How many touches does one virtual card reimbursement require—end to end?
- Exceptions: What percentage of payments end up in unapplied cash, rework queues or write-off discussions?
- Risk: How many people, and which roles, can currently access or handle virtual card credentials?
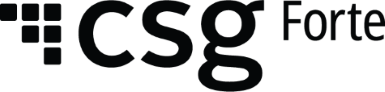
- Readiness: Which specialties or locations are best suited for a 90-day pilot, based on volume and operational pain?
If the honest answers describe a process driven by envelopes, portals, terminals and spreadsheets, you’re squarely in the zone STP is designed to address.
Next step: move virtual card reimbursements from manual to straight-through
Virtual card payments are not going away—and for many physician groups, they represent a significant, growing share of otherwise reliable payer revenue. The question is whether that revenue continues to move through paper-era workflows, or through straight-through reimbursement that supports your cash, cost and control goals.
Straight Through Processing with Optum and CSG Forte offers a path to:
- Replace mail and portals with automated, next-day deposits
- Move from keying every payment to managing a defined set of exceptions
- Tighten controls and audit trails across payers, specialties and locations
- Free your teams to focus on strategy, relationships and growth—not manual posting
To see how STP could fit your physician group’s reimbursement strategy, visit the Optum + CSG Forte STP page and explore a pilot program that’s tailored to your payer mix.
Frequently Asked Questions
1. What are virtual card reimbursements in healthcare?
Virtual card reimbursements are payer-funded card transactions generated for approved claims or patient balances. Instead of sending a paper check, the payer (or an intermediary such as Optum) issues a single-use card credential that the provider processes like a card payment.
2. Why do virtual card payments create so many posting headaches for physician groups?
Because card credentials and remittance details rarely arrive as one clean, machine-readable package. Staff must retrieve card numbers from mail or portals, run them through terminals, then manually match deposits to 835s or PDFs across systems—creating delays, errors, unapplied cash, and “mystery deposits” at close.
3. What is Straight Through Processing (STP) for virtual card reimbursements?
STP is a payment automation model where payers still generate virtual cards, but card and remittance data move electronically to CSG Forte for automatic processing and deposit. Funds are routed directly to the provider’s bank account and paired with aligned remittance data that supports auto-posting and cleaner reconciliation.
4. Does STP replace ACH EFT for reimbursements?
No. STP is focused on automating virtual card reimbursements—including insurer payments and patient-via-payer portal payments. Many providers run ACH and STP side by side: they request EFT/ERA via ACH where it is available and use STP to handle the growing share of virtual card volume that is unlikely to disappear.
5. How can a physician group evaluate whether STP is worth piloting?
Start by quantifying virtual card volume, staff minutes per payment from “payment available” to posted, effective fee rates, exception rates, and unapplied cash tied to those streams. High-volume, high-friction payer or specialty cohorts—where lag and rework are heavy—are strong candidates for a 60–90-day STP pilot. It’s also a good move to check out this practical guide we put together specifically to help physician groups.