A Practical Model for Digital Payment Risk Management
Key Takeaways
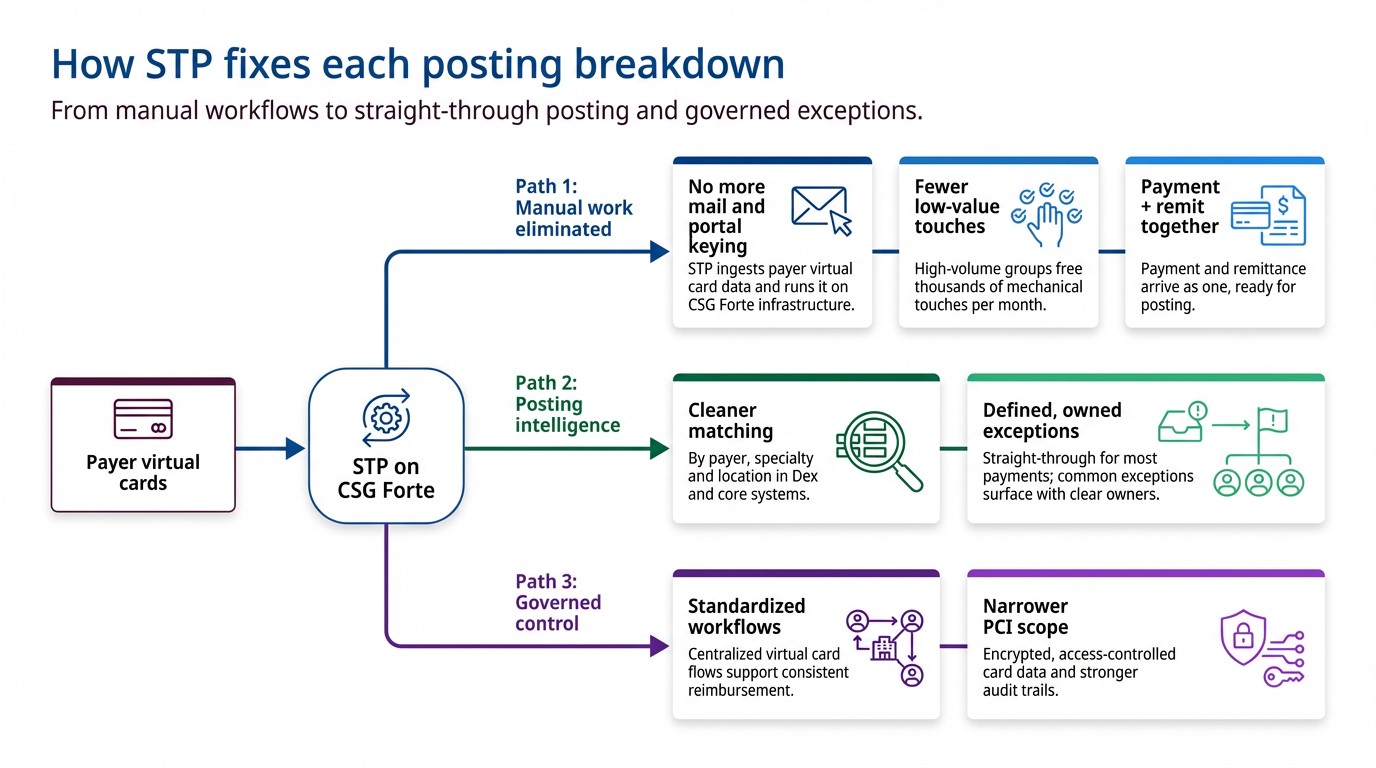
- Online payments are now a primary fraud battleground: As more bill pay and customer transactions move online, attackers are targeting these flows with sophisticated scams, making fraud protection a front-line business priority, not a back-office concern.
- AI has raised the stakes on both sides: Fraudsters now use AI to automate attacks (ATO, synthetic identities, phishing), so businesses need AI-driven tools to keep up.
- Modern fraud protection must be adaptive and transparent: The strongest defenses deploy quickly, learn from your unique transaction patterns, and give you clear visibility and controls so you can cut fraud and false positives without slowing good customers down.
Digital payments are a growth engine, but only when you can keep good customers moving and bad actors out. That’s the real job of payment risk management: reducing fraud losses and reducing unnecessary friction (false declines, delayed approvals, and customer support fallout). Traditional tools often fall short because they’re slow, siloed, hard to tune, and can create as many customer experience issues as they prevent.
Why payments need a clear risk model
A clear risk model matters because payment risk isn’t one problem—it’s a chain reaction:
- Fraud losses hit margin directly (plus chargebacks/returns, fees, and write-offs).
- False positives hit revenue indirectly (blocked transactions, abandoned checkouts, churn, and a spike in “why was my payment declined?” support tickets).
- Compliance expectations keep rising, especially in ACH fraud monitoring and card-network dispute/fraud programs.
A practical risk model gives you three things most teams don’t have today:
- A shared definition of “acceptable risk” (so teams stop fighting over one-off decisions).
- A map of where risk enters your payment flows (so you can fix root causes, not symptoms).
- Repeatable operating rhythms (so improvements don’t disappear after the next incident).
If you want a familiar structure to align security and fraud teams, the National Institute of Standards and Technology recommends lifecycle framing—Identify, Protect, Detect, Respond, Recover—as a useful backbone to adapt to payments.
Mapping your main payment and fraud risks
Start by mapping risks across the full payment lifecycle (not just the authorization moment). A simple way to do it is to build a one-page “risk register” by journey stage:
1. Account & login (before a payment happens)
Common risks: Account takeover (ATO) via phishing, credential stuffing, or social engineering and refund redirection (fraudster changes payout details, then triggers refunds/credits).
2. Payment setup (adding or updating payment methods)
Common risks: Bad payment data and mismatched account ownership (drives downstream declines/returns and customer friction).
3. Transaction attempt (authorization + post-auth monitoring)
Common risks: Card testing (small, high-velocity attempts to find valid cards), customer payment fraud, excessive payment / refund abuse.
4. Merchant/portfolio risk (especially for ISVs, aggregators, multi-location orgs)
Common risks: Merchant bust-out fraud and merchant credit events/defaults.
5. Settlement, disputes, and recovery (after the payment)
Common risks: Chargebacks/disputes, ACH returns, and “friendly fraud” patterns that look like legitimate customer behavior until you zoom out across history.
6. Financial crime and compliance exposure
Common risks: AML red flags and related reporting/compliance obligations.
A quick way to prioritize
For each risk, score four dimensions (1–5 is fine):
- Impact (loss size + fees + operational load)
- Likelihood (frequency)
- Speed (how fast it causes damage)
- Customer friction risk (how likely a control will block good customers)
That last line—friction risk—is what connects payment risk management directly to growth and retention. Your goal isn’t “lowest fraud at any cost.” It’s lowest fraud with the highest approval rate you can safely maintain.
Prevention, detection, and response: the core layers
A workable program uses a layered security model. If one of the three layers is weak, the others get overloaded.
Layer 1: Prevention (reduce exposure up front)
Focus prevention on high-leverage moments—places where a small amount of friction prevents a lot of downstream loss:
- Risk-based authentication for login, payment method changes, and refund destination changes
- Limits and velocity controls (by user, device, account, instrument, and channel)
- ACH-specific monitoring expectations: Nacha’s ACH Fraud Monitoring Requirements raise expectations for formalized procedures and continuous monitoring (with phased effective dates called out in CSG materials)
- Data protection and incident readiness (especially for card data environments). PCI DSS requires an incident response plan as part of the standard
Layer 2: Detection (spot bad patterns fast—without over blocking)
Detection is where many programs break down because signals are split across payment rails and channels. Modern detection should aim for:
- Cross-channel monitoring across ACH and cards, and across online/phone/in-person flows.
- Near real-time alerting and decision support, so you can intervene before settlement cutoffs when possible.
- Ongoing tuning as patterns evolve—because attackers adapt quickly, and static rules alone tend to either miss new fraud or spike false positives.
Layer 3: Response (make decisions consistently, at speed)
Response is not just “review the alert.” It’s a set of pre-approved actions with clear owners and SLAs, such as:
- Auto-decline or auto-hold for transactions above defined thresholds
- Step-up verification for suspicious but salvageable activity (to save good payments)
- Void/cancel before settlement where applicable (especially when alerts arrive within operational windows)
- Case escalation paths (front-line ops → fraud specialists → finance/legal/compliance as needed)
Building cross-functional ownership and processes
Payment risk management fails when it’s treated as “the fraud team’s job.” Fraud is a system issue spanning customer journeys, product decisions, data, and operations.
A practical ownership model usually includes:
- Payments/Product: defines customer journeys, acceptable friction, and high-risk flows
- Fraud/Risk Ops: owns strategies, rules/thresholds, investigations, and playbooks
- Finance: quantifies loss, ROI, reserves, and chargeback/return exposure
- Engineering/Data: instrumentation, data quality, model inputs, and integration reliability
- Customer Support: closes the loop on false declines, disputes, and customer impact signals
Two processes make the biggest difference:
1. A rules/threshold change process (with guardrails)
Treat changes like product releases: request → evaluate expected impact → test/roll out → measure → iterate.
2. A documented escalation and decisioning process (with SLAs)
If you don’t define SLAs, your “response layer” becomes random:
- Who decides?
- How fast?
- What happens if capacity is exceeded?
- What’s the fallback (auto-approve, auto-decline, queue)?
Below is a straightforward example of an operational workflow you can copy: thresholds → monitoring → escalation → reporting → tuning.
Metrics and reviews that keep the program on track
If you only track fraud dollars, you’ll eventually “solve” fraud by declining too much good volume. Track balanced metrics in five buckets:
1. Loss and liability
- Fraud loss rate (pre/post changes).
- Chargeback and dispute rates (and $ impact).
- ACH return rates (unauthorized/administrative/general).
2. Customer friction (growth & retention indicators)
- False positive rate (and leading indicators like cart abandonment or support contacts).
- Approval rate uplift / revenue impact tied to better decisioning.
3. Operational performance
- Time to decision and % auto-declines within thresholds.
- Alert volume vs. analyst capacity and SLA adherence.
4. Control health
- Rule hit rates, watchlist growth, top drivers by channel/rail, and “what changed since last month?” (so you catch drift).
5. Compliance readiness
- Evidence that monitoring and procedures are documented and consistently followed (especially important as ACH monitoring expectations increase).
Review cadence that actually works
- Daily: spikes in declines, chargebacks, returns, and top alert drivers.
- Weekly: rule/threshold adjustments, escalation backlog, “top 3 fraud patterns this week.”
- Monthly: KPI scorecard (loss + friction + ops), plus a tuning plan.
- Quarterly: risk appetite check-in (are you optimizing for growth, margin, or both?), plus a tabletop exercise for a major incident.
Where Payments Protection.ai fits (and why it’s relevant in consideration)
Once you’ve got the model, the question becomes: do you have the tooling and support to run it consistently?
CSG Payments Protection.ai is an AI-driven fraud detection and financial risk management solution designed to monitor ACH and card transactions across online, phone, and in-person channels, using an AI/ML-powered rule engine with custom thresholds to auto-decline, flag, and escalate cases.
It also supports a managed approach with CSG analysts for decisioning, plus periodic tuning and reporting.
It’s also positioned around outcomes that map directly to a growth-and-retention lens: reducing fraud losses while reducing false positives and customer friction, with KPIs like fraud loss rate, false positive rate, time-to-decision, and approval rate impact.
If you’re evaluating options, a practical next step is to run a short assessment using the framework above—then map your highest-priority journeys and risks to the controls, workflows, and KPIs you’ll need to operate at scale.
If you want to see how this model applies to your payment flows (and where you’re likely over- or under-controlling), explore CSG Payments Protection.ai and request a walkthrough focused on your channels, rails, and top fraud vectors.