How a Layered Strategy Helps Prevent Account Takeover Fraud in Digital Banking
Top Takeaways
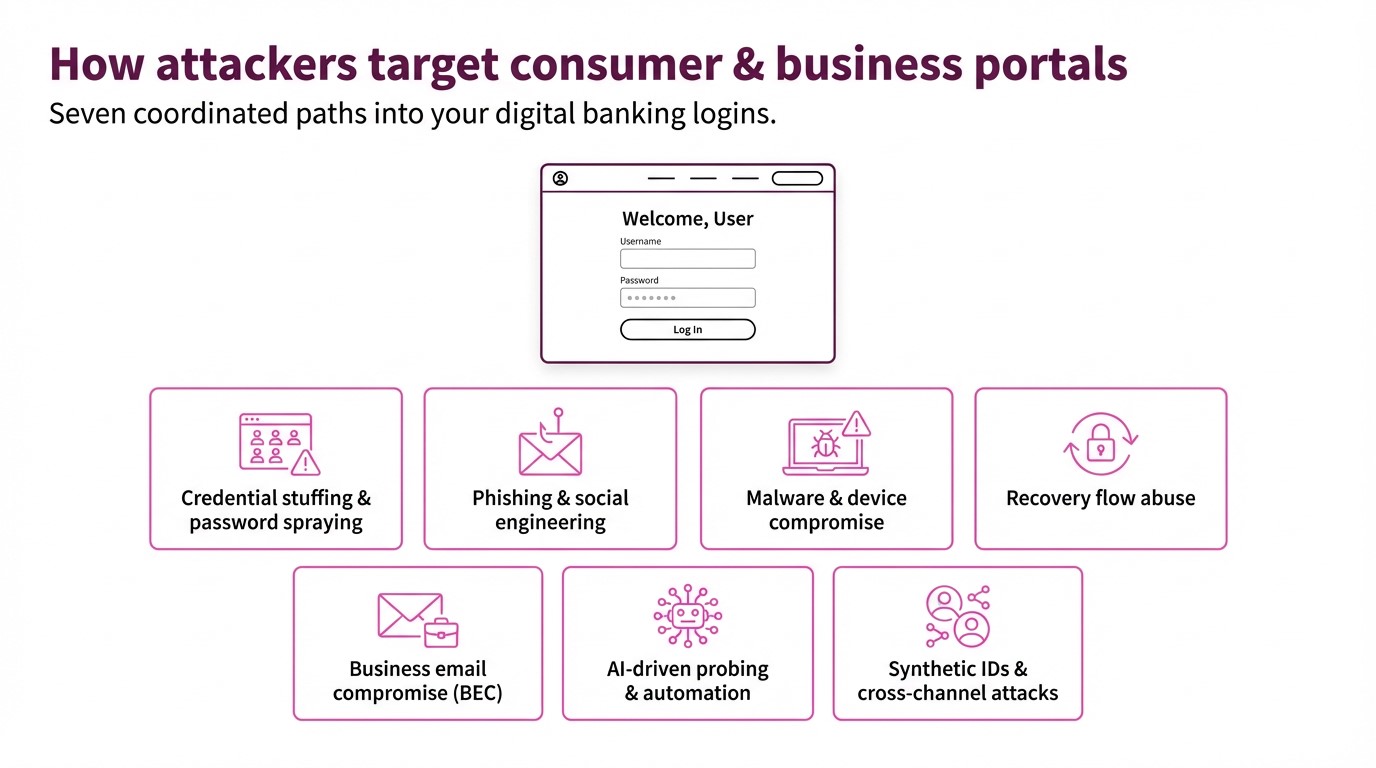
- Account takeover fraud in banking is growing as attackers automate credential abuse and exploit weak portal controls.
- A layered defense blends smarter authentication, continuous risk-based monitoring and coordinated fraud operations.
- Banks that pair internal fraud teams with AI-powered partners can cut losses while keeping customer experiences fast and friction-light.
A customer logs into their online banking portal, just like they do all the time. It looks the same as it always does, but what they’re not seeing is that someone else has already logged in. Behind the scenes, a fraudster has changed the user’s email address, added a new device, and initiated a series of high-value transfers.
That is account takeover (ATO) fraud: Identity-based attacks that turn trusted banking portals into launchpads for theft.
And as digital banking usage grows, so does the risk. Between 2023 and 2028, global online payment fraud losses are expected to exceed $362 billion, with $91 billion in 2028 alone, according to Juniper Research. Which is exactly why financial firms cannot afford to treat ATO fraud as a niche threat. It is now one of the fastest, most damaging paths from compromised credentials to lost funds and eroded trust.
This article explains how ATO threatens consumer and business portals, and outlines a practical, layered defense strategy that’s anchored in having a modern, secure payments portal, and aligned to how banks operate today.
Why account takeover is a critical risk for banks
ATO fraud happens when a bad actor gains control of a legitimate customer or business account and uses it to move money, harvest data, or pivot into other parts of your environment. It’s clear why that’s harmful to the banking customer, but from the business perspective, that can mean:
- Draining consumer checking or savings via Zelle, RTP, wires or bill pay
- Hijacking treasury portals to originate ACH batches or cross-border payments
- Issuing unauthorized refunds or credits to mule accounts
- Changing contact details to intercept step-up challenges and alerts
Because many of these payment rails are real-time or near real-time, losses are hard or impossible to claw back. The impact on your organization isn’t just the losses from financial write-offs; it’s the hit to your reputation, your customers’ trust, and the increase in regulatory scrutiny that directly undercuts growth and retention objectives.
With ATO fraud, banking teams can’t afford a purely perimeter mindset. You need to assume some logins will be compromised and design defenses that detect and contain misuse quickly.
Strengthening authentication without breaking UX
The first impulse with ATO is to lock everything down for safety. But to users, that “safety” translates to more friction. If authentication becomes painful, customers abandon digital channels—or your bank entirely.
A better approach is adaptive, risk-based authentication.
Modern multifactor identification (MFA), selectively applied: Use phishing-resistant factors and reserve step-up challenges for higher-risk situations: new devices, unusual geolocation, or sensitive actions like adding payees or changing contact details.
Device and session intelligence: Recognize known, low-risk devices and browsers so you can streamline their experience while scrutinizing new or suspicious fingerprints more closely.
Behavioral signals: Look at impossible travel, abnormal typing cadence, navigation anomalies, or machine-like interaction patterns as inputs into your risk score.
Crucially, these controls work best when they’re informed by downstream payment-risk data, not just login metadata. If your fraud engine sees rising disputes, ACH returns or unusual limit hits tied to a subset of accounts, you can tighten authentication for that cohort rather than the entire customer base.
Using risk-based monitoring to catch ATO early
Even with strong auth, some ATO attempts will succeed. The next layer is continuous, risk-based monitoring across your payment flows and account activity, tuned specifically to ATO behaviors, such as:
- First-time or high-value payments to new beneficiaries
- Unusual changes to limits, contact details or authentication factors
- Sudden shifts in channel mix (e.g., a branch-only customer sending a flurry of RTPs from a new device)
- Patterns of small “test” payments followed by large transfers
Here, banks benefit from AI/ML-powered monitoring and configurable rules that operate across ACH, card and digital wallets, and across online, mobile, phone and in-person channels.
Solutions like CSG Payments Protection.ai ingest transactions in near real time and apply adaptive rules and models to flag anomalies, auto-decline clearly high-risk events, and escalate borderline cases to analysts—all before settlement cutoff times.
Because Payments Protection.ai monitors every transaction—not just those already suspected as fraud—it can:
- Minimize financial losses and maintain customer trust by catching suspicious activity early.
- Significantly reduce false positives, using industry-tuned rules and models so you’re not blocking good customers in the name of safety.
For banks wrestling with real-time rails, that combination—coverage, speed, and precision—is essential.
Partnering with fraud and payments vendors effectively
Most banks already have fraud tools in place. The challenge is that many are fragmented, slow to adapt, and hard to customize.
To upgrade your ATO defense without ripping and replacing your stack, look for a partner who can:
- Cover your full payment mix: ACH, cards, and digital wallets across online, phone, branch and in-person channels, with a single, coherent risk view.
- Adapt in real time: AI- and rules-based engines that learn from every transaction and quickly absorb new fraud patterns and regulatory expectations (e.g., Nacha ACH fraud monitoring, card-brand thresholds).
- Balance automation with expert oversight: Options for fully managed decisioning or shared workflows, plus consultative tuning of thresholds and watchlists over time.
- Scale and secure: Cloud-based, PCI-compliant platforms with near-perfect availability that can handle spiky payment volumes without delaying decisions.
CSG Payments Protection.ai was built with those criteria in mind. It brings:
- 20+ years of payments expertise, processing over 215 million transactions and $164B in payment volume annually for 150k+ merchants, giving deep behavioral insight into how legitimate and fraudulent payments behave
- Documented results, where clients using the underlying technology have seen fraud-loss reductions of 50–70% and extremely low false-positive rates
- Fraud detection and payment processing services with industry-leading uptime—empowering banks to operate securely and efficiently, no matter the volume or demands.
For banks, that kind of partner can turn ATO detection and prevention from a cost center into a growth and retention lever: protecting digital adoption, keeping payment experiences smooth, and reinforcing the trust that keeps customers from shopping their relationship.
A layered approach—strong but adaptive authentication, continuous risk-based monitoring, and the right fraud-prevention strategy—gives your bank a realistic path to stay ahead of account takeover fraud in banking portals.
With ATO fraud on the rise and attackers always looking for new paths into your banking portals, now is the time to shore up your account takeover defenses. To see how Payments Protection.ai can fit into your ATO strategy, request a conversation today with the security experts at CSG Forte.
Frequently Asked Questions
What is account takeover fraud in banking?
Account takeover (ATO) is when a fraudster gains unauthorized access to a legitimate customer or business banking account—often via stolen or phished credentials—and then initiates payments, changes contact details, or harvests data as if they were the real accountholder.
Why are bank payment portals such a high-value target for ATO?
Online and mobile portals sit at the intersection of identity and money movement. Once an attacker controls a login, they can move funds, redirect refunds, change notification methods, and enroll new devices, often before traditional controls notice anything is wrong.
How can banks strengthen authentication without frustrating customers?
The most effective approach is adaptive or risk-based authentication. Instead of forcing step-up friction on every login, you selectively add challenges when behavior, device, location, or transaction patterns look unusual. That keeps everyday logins fast but adds security when risk rises.
What does “risk-based monitoring” mean in the context of ATO defense?
Risk-based monitoring means analyzing transactions and account activity in near real time to score risk and trigger actions—such as step-up authentication, holds or manual review—based on patterns that indicate ATO, like sudden changes in device, IP, payment amounts, or refund behavior.
Where does a solution like CSG Payments Protection.ai fit?
CSG Payments Protection.ai provides AI/ML-powered, near real-time monitoring across ACH, card, and digital wallet transactions, reducing false positives and adapting to new fraud patterns as they emerge. It’s designed to help banks detect ATO, card testing, and other payment fraud vectors without slowing down legitimate payments.